Canon has 5% of its stolen data leaked online (report)
Canon USA was allegedly subject to a hacker attack with 10TB of data stolen – now 5% of that data has been leaked

UPDATE 02/09: After the alleged hacker attack on Canon USA last month, there have now been reports that 5% of the data stolen has now been leaked. Canon USA was hit with this attack by the Maze ransomware gang, with many of their services affected, including their email, Microsoft Teams, the Canon USA website and other internal applications.
Canon USA also had 10TB of data stolen (although this appears to be internal data and not users' photos or videos). Bleeping Computer, the site that first ran the story on Canon's hack, has given an update on the situation.
• Read more: Best Canon camera
"Maze is an enterprise-targeting human-operated ransomware that compromises and stealthily spreads laterally through a network until it gains access to an administrator account and the system's Windows domain controller. During this process, Maze will steal unencrypted files from servers and backups and upload them to the threat actor's servers…
If a victim does not pay the ransom, Maze will publicly distribute the victim's stolen files on a data leak site that they have created."
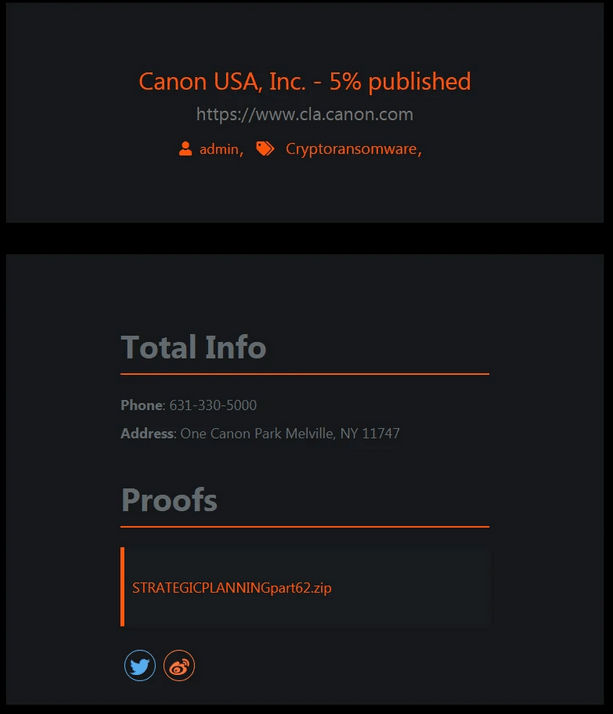
It now seems that this might be the case, as Bleeping Computer has reported that a 2.2GB archive called 'STRATEGICPLANNINGpart62.zip' was released on the Maze data leak site. Bleeping Computer has been told that it contains marketing materials, videos and other files related to Canon's website. However, apparently the leak does not contain any sensitive data, such as financial or employee information.
Whether this will motivate Canon to pay Maze's ransom remains to be seen, but we will update this story with more information as the situation continues to unfold.
The best camera deals, reviews, product advice, and unmissable photography news, direct to your inbox!
• Read more: Best antivirus software
UPDATE 10/08: Canon has announced the results of its investigation into the loss of image data on the image.canon cloud platform. According to Canon, when the company switched over to a new version of the image.canon software on 30 July, the code to control the short-term storage operated on both the short-term storage and the long-term storage functions, causing the loss of some images stored for more than 30 days.
On 4 August, Canon was able to identify the code causing the incident and corrected it. Canon has now reported that it found no unauthorized access to image.canon and the incident caused no leakage of images.
Canon has said that there is no technical measure to restore lost video files, but that photo files can be restored – albeit not at their original resolution. This means that if the affected users have not backed up their files, then they will have lost them forever. Canon has said: "We will contact affected users shortly and offer our deepest apologies".
ORIGINAL STORY:
Canon may have been hit with a ransomware attack from Maze, impacting several services including Canon's email, Microsoft Teams, USA website and other internal applications. According to this article from Bleeping Computer, a ransomware attack from Maze has resulted in the loss of data, private databases and more.
Bleeping Computer were first tipped off to this potential hack when the image.canon site had an outage on 30 July, 2020, which lasted for six days until it went back into service on 04 August, 2020. Bleeping Computer first started investigating this outage after the final status update said that while some of the photo and video files saved in the 10GB storage had been lost, "there was no leak of image data".
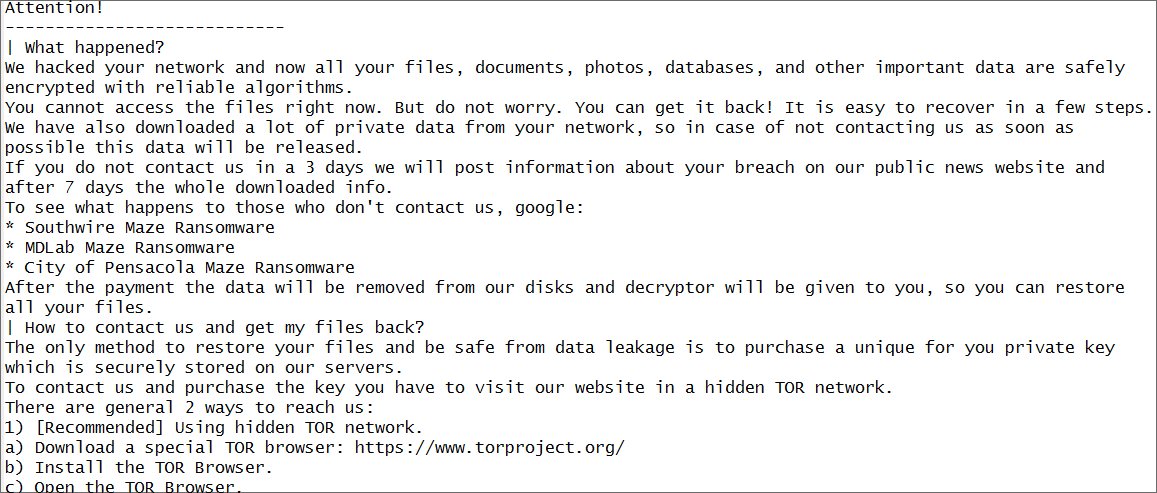
Through some investigation, Bleeping Computer was eventually able to get their hands on a partial screenshot of the alleged Canon ransom note. This note claimed that "We hacked your network and now all your files, documents, photos, databases, and other important data are safely encrypted with reliable algorithms. You cannot access the files right now. But do not worry, you can get it back!… The only method to restore your files and be safe from data leakage is to purchase a unique for you private key…"
Bleeping Computer contacted the ransomware operator Maze and was given confirmation that the group was behind the attack. Bleeping Computer explains the group as "an enterprise-targeting human-operated ransomware that compromises and stealthily spreads laterally through a network until it gains access to an administrator account at the system's Windows domain controller… Once they have harvested the network of anything of value… Maze will deploy the ransomware throughout the network to encrypt all of the devices".
If the cyberattack victim doesn't pay the ransom, Maze will then publicly distribute the stolen files on their own data leak site. In a statement to Bleeping Computer, Canon said that they are "currently investigating the situation", so we will have to wait and see how the story develops…
Read more
Hands on: Canon EOS R5 review
Hands on: Canon EOS R6 review
Canon EOS R5 vs R6: What are the differences and which is best for you?
With over a decade of photographic experience, Louise has a wealth of knowledge on photographic technique and know-how – something at which she is so adept that she's delivered workshops for the likes of ITV and Sue Ryder. Louise also brings years of experience as both a web and print journalist, having served as features editor for Practical Photography magazine and contributing photography tutorials and camera analysis to titles including Digital Camera Magazine and Digital Photographer, as well as previously working as Digital Camera World's ecommerce editor. Louise currently shoots with the Fujifilm X-T200 and the Nikon D800, capturing self-portraits and still life images.


